Accept Hackers’ Terms and Conditions?
Education Cybersecurity Weekly is a curated weekly news overview for those who are concerned about the Education industry. It provides brief summaries and links to articles and news across a spectrum of cybersecurity and technology topics that are specific to the industry.
Starting around the first of the year, global spam volumes dropped by nearly 50%. This news could have been positive unless attackers were repurposed as cryptominers. Generally, we can keep calm – The Fifth Element scenes unlikely will come true.Again. UK cybersecurity universities became a target for Iranian hackers
Techradar.pro on October 30, 2018
The previous week’s breaking news refers to Iranian hackers. For now, they attempted to hack into UK top-flight cybersecurity universities. Malefactors targeted at least 18 British universities, including institutions certified by the National Cyber Security Center (NCSC) that provide degrees in cybersecurity.
Attackers chose an effective way of getting students’ credentials. They sent phishing emails tricking recipients into giving up their passwords. Fortunately, a small number of students fell for the attack.
The attacks are believed to be linked to a previous campaign in which dozens of universities were hacked and their research was published on two Iranian websites.
Support this site by sharing your computer? 3 ways to avoid cryptomining in K–12 sector
EdTech on November 1, 2018
Starting around the first of the year, global spam volumes dropped by nearly 50%. This news could have been positive unless attackers were repurposed as cryptominers.
Thus, here are three actionable tips for handling this newest menace:
- Everything you already know still mostly applies.
- Network-based protections help but don’t solve the problem.
- DNS-based protections may be a good addition.
Although cryptomining is just another kind of malware and common anti-malware tools are suitable, K–12 IT managers should review their anti-malware tool lists because not every instrument is able to detect and block in-browser attacks.
One of the effective methods is to use network-based Intrusion Prevention Systems (IPSes) to identify outbound connects and block that traffic. However, the system will remain infected, if a specialist doesn’t clean it up.
And what is important, K–12 IT managers who have already chosen to implement DNS-based filtering should enable cryptomining categories for their school.
What robots can never replace
EdSurge on November 5, 2018
An interesting point of view on the robots’ impact on the employment landscape is described in EdSurge. Generally, we can keep calm – The Fifth Element scenes unlikely will come true.
In fact, what we do effortlessly as humans may be least susceptible to automation. For instance, riding a bike or cracking an egg on the side of a bowl are hardly could be described in computing, these skills lie beneath the consciousness. Moreover, at a recent EmTech Next conference roboticists claimed how difficult it is to teach a robot how to grasp an object and simply adjust its grip.
Another sector where robots lost to the man is hiring process – AI algorithms are not able to consider all factors of applicant’s experience. Thus, when it comes to sensorimotor-specific, social or emotional work, humans will remain the best employees.
Checklist before trying new edtech in the classroom
EdScoop on October 30, 2018
It is better to prevent cybersecurity threats rather than face them. Have a look at 5 aspects to mention before implementing new technology in the classroom:
- Don’t sign up for an app or service without checking with your school/district. It is especially actual for the use of social media in the education process because it should correlate with school and district’s use policies.
- Don’t assume an app or tool is safe to use in the classroom just because you heard about it at a conference.
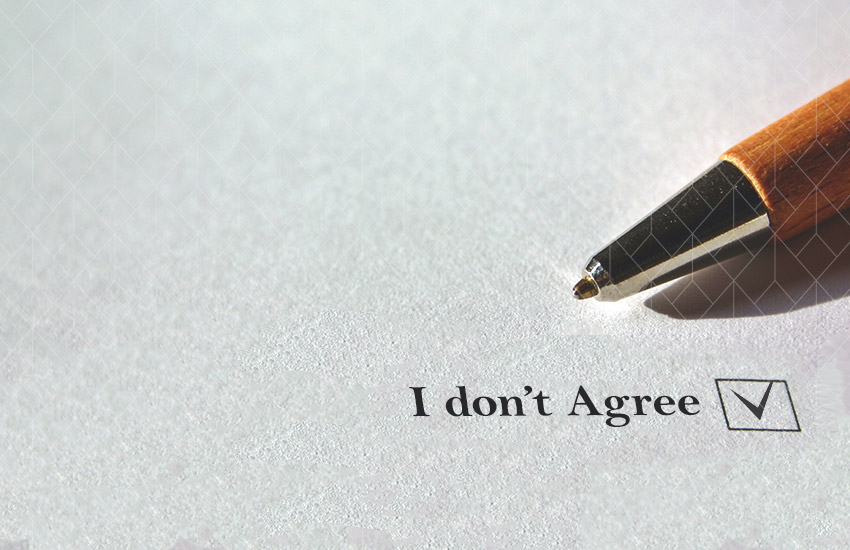
- Understand the implications of “clickwrap agreements.”
- Read the terms of service and the privacy policy.
- Educate yourself about student privacy.
For example, voice-activated assistants such as Amazon Echo and Google Home are not designed to comply with Children’s Online Privacy Protection Act (COPPA) and the Family Educational Rights and Privacy Act (FERPA). Therefore, teachers shouldn’t use them.
Clicking the button “agree” to a long list of terms, the teacher enters into a legally binding contract on behalf of students and school, so every click should be conscious.
If you understand the privacy policy and believe it does not violate federal or state law, but your school or district does not approve apps, you should send a letter home to parents, informing them of the apps used in your classroom.
Final and the most important aspect. The list of useful resources is in the article.
